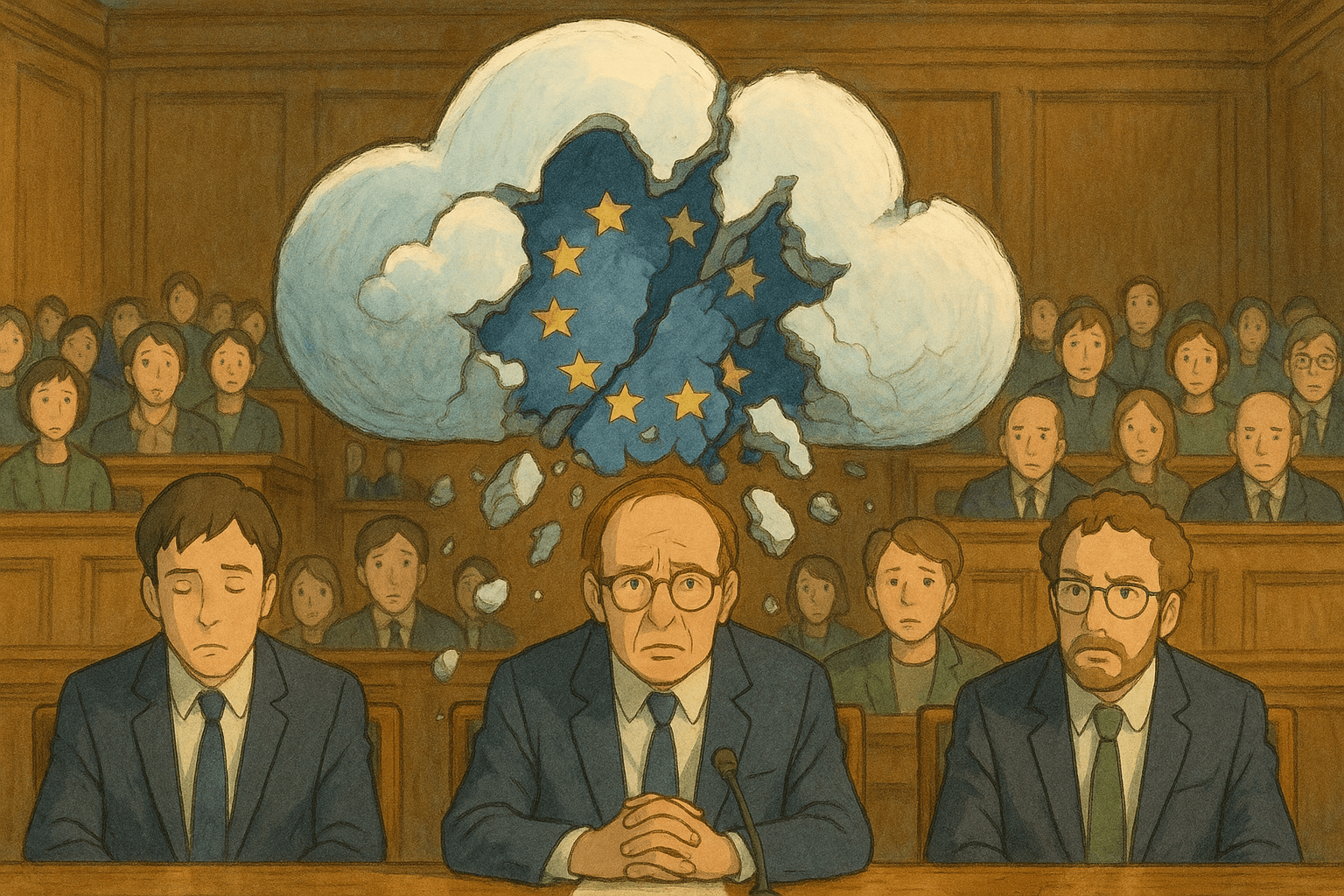
Big Tech’s 'Sovereign Cloud' Promises Collapse
The recent collapse of Big Tech's 'sovereign cloud' narrative reveals the gap between marketing and legal realities. Executives testifying under oath about failing to shield European data expose the truth behind 'digital sovereignty'.